What is personal data exactly? The term “personal data” can mean different things to different people. When it comes to how attackers – the folks we used to call “hackers” – can find it and what they can do with it, there are some things that everyone needs to know about their personal data, and how to protect it.
So, what? You might be thinking. It’s my email and birthdate. They can have it!… It seems like everyone has it already.
But just because it is out there doesn’t mean you shouldn’t try to maintain control of your data. Even little pieces of information in the wrong hands can give attackers enough power to find even more information to eventually lead to their goal of taking money through ransom, fraud or just selling access to it.
But it’s not all a lost cause, as there are strategies to avoid letting things get to this stage with any new attack method. Why make it easier for them to cause you financial losses and frustration?
The first step is knowing what personal data really is and how to protect it while online, which we’ll be covering in this article.
About personal data
What does personal data look like?

"It’s been a “super-fantastic” experience to see people learning and talking about security threats."
For just $325 USD, you can run a 6 week, automated program for gamified phishing awareness training and challenges. (Limited time offer. Normally valued at $999 USD)
Use Promo Code: 6WEEKS
Personal data actually refers to much more than just your email and birthdate. Personal data is any information that can be used to identify you, your associations or your activities. This includes your name, address, phone number, email address, groups you belong to, things you like or don’t like, location data, and even your credit card number (often an attacker’s golden ticket).
What can attackers do with it?
By obtaining one little piece of personal data, they can potentially access more pieces of information through other websites. With big data breaches, most attackers take all your data and sell it to more criminals.
Other attackers may use your information to access your credit cards and bank accounts to take money, impersonate you on social media to get money from other people, or hold information or accounts for ransom.
How can we protect personal information on social media?
As mentioned in a recent blog post, social media is a great way to stay connected but is also a major hunting ground for online hackers. The most important thing for protecting your personal information on social media is to have different passwords for each different account.
But, I’ll forget my password! I like having one password for everything so I never have to guess.
You don’t actually have to remember hundreds of passwords for all your different websites and social media accounts. That’s why there are trusted password managing platforms where you can create one extremely strong password that holds all your other randomly generated, complex, unique passwords.
This way, if your personal data is ever breached on social media, the attacker won’t automatically gain access to everything stored in other accounts you own.
How do we protect personal information while online shopping?
There are two major opportunities for attackers while you are shopping online or using different websites:
- Targeting companies that hold lots of information. The healthcare industry has paid the highest costs for data breaches in the past ten years. You can imagine why these companies are targeted so much: they hold valuable information that attackers can easily sell. Other examples would include banks and password managers.
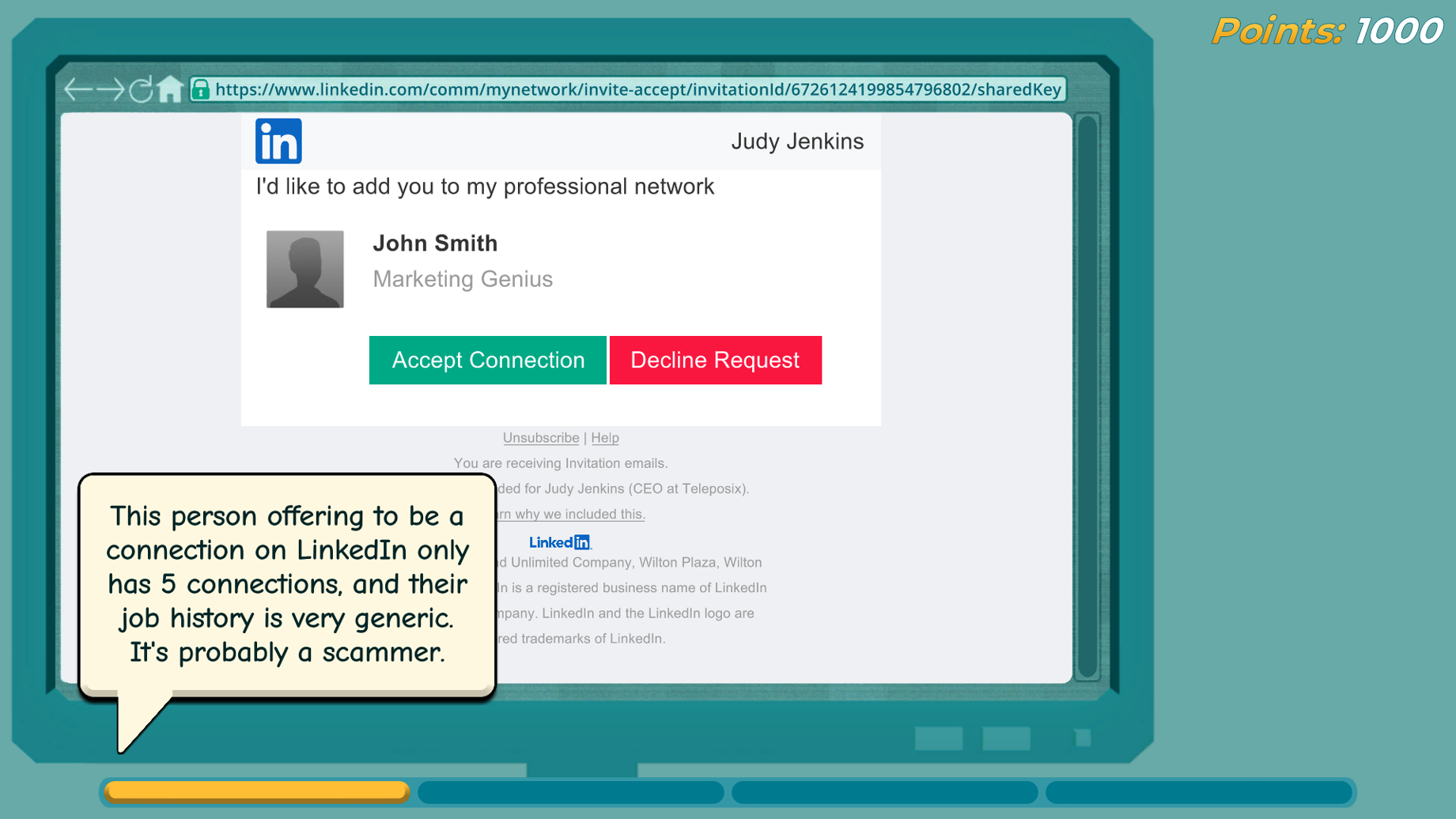
- Luring you to a website, pretending to be a company that you trust. Sometimes, attackers don’t need to even get involved with other companies to obtain personal data. They can set up websites that look real or trustworthy (or sometimes that look exactly like your favourite website) and get you to put in your information there.
For the first type of company, it’s incredibly hard to predict whether or not a company will have a data breach in the future. The LastPass breach is a great example of this; many cyber security professionals trusted this brand with their passwords, and it still was breached. The best thing you can do is to review the latest security practices of the companies you commonly shop at to see if it’s something you are comfortable with. Using different passwords for each account is essential to help prevent data breaches affecting multiple online accounts.
To protect yourself from impersonation websites while shopping online, always ensure that the website you’re using is secure (look for the “https” at the beginning of the URL) and only use trusted payment methods such as PayPal or Apple Pay when making purchases online. Never use wire transfers such as Western Union for payments to online entities you don’t know are really trustworthy, and make absolutely sure they are who they are claiming to be. You should also delete any online purchase receipts once you’ve completed a transaction as these can be used by criminals to gain information that may make it easier to target and access to your accounts, or steal your identity.
How do we protect personal information for our customers and employees?
If you run a business or are an employer then it’s important that you take steps to protect your customers’ personal data from falling into the wrong hands. Unsafe security practices can lead to breaches that spread across a corporate network and put customers’ personal and sensitive data at risk.
You should train employees to not only know what’s personal data, but also on cyber security best practices such as never sharing passwords or sensitive information over unsecured connections (such as public Wi-Fi).
A common statement made by some security managers is: “It’s frustrating to try to train employees, because no one seems to care or pay attention to our security awareness training. They find it too boring.”
Is your training engaging? Employee engagement increases by 80% when it’s gamified. By making the training videos interactive, shorter over a longer period of time, and applicable to each employee’s situation, engagement and participation rates will significantly increase. Even better, employees will have retained more knowledge, and they will be better at protecting your customers’ personal data.
use Click Armor gamified training creates a more positive security culture within your company. You can book a call with us to get a demo for your business.
You should also ensure your organization has a balance of security training, processes and technologies. It is certainly important to have security software solutions that monitor employee activity and alert you if there is any suspicious activity detected on company networks or devices. No single type of security safeguard or control is 100% reliable. If you don’t provide your employees with the resources they need to protect the network and systems you are putting customer and employee personal data and your business data at risk.
What if my personal data is breached?
How to know
If your personal data is breached through a company or website being attacked or exposed, the organization that was breached should put out a statement regarding the situation. If you think you may have missed previous announcements, you can check websites like Have I Been Pwned? to see which breaches your email and other information may have been included in.
What to do if your personal data has been affected by a security breach
There are steps to take after you’ve realized your data has been breached:
- Change all your passwords. The password that was breached, any ones that are the same as that, and the general password to your password manager. (NOTE: You should never use the same password on multiple accounts, but it may have happened in the past.)
- Check for any updates from the company. They may give additional information on what to do.
- Monitor the situation. Monitor your bank accounts, social media accounts, and shopping accounts for any suspicious activity.
- Consider freezing your credit cards. This may not be necessary, but if the breach was closely related to your financial information, you may want to consider this.
- Obtain a detailed credit report. Credit bureaus such as Equifax and TransUnion maintain information about your loans and other credit accounts. A credit report from them can help you identify whether your account and credit history are being impacted by unauthorized transactions.
Learning more about hackers and what they can really do with your information can feel scary. But, there’s a growing community of cyber security professionals that are working to create better solutions for protection and raise awareness about these issues.
By understanding what constitutes personal data and taking steps such as setting strong passwords, using secure payment methods when shopping online, investing in effective training for business, and taking the proper steps after a breach we can all help ensure our sensitive information remains safe from those who would seek to exploit it for their own gain.
With this knowledge in hand, we can more confidently use online systems, knowing that we are doing all we can to protect our own personal data, as well as that of our customers!
Scott Wright is CEO of Click Armor, the gamified simulation platform that helps businesses avoid breaches by engaging employees to improve their proficiency in making decisions for cyber security risk and corporate compliance. He has over 20 years of cyber security coaching experience and was creator of the Honey Stick Project for Smartphones as a demonstration in measuring human vulnerabilities.


