Engage your employees with interactive security training
Click Armor boosts your human risk management program with...
Engage your employees with interactive security training
Click Armor boosts your human risk management program with...
Test your phishing skills now!
Start
Transforming Cybersecurity Awareness: Interactive, Gamified Learning for Effective Employee Resilience to Attacks
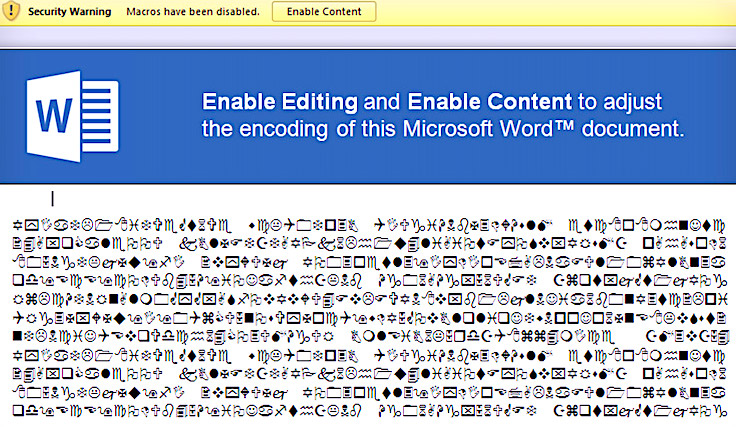
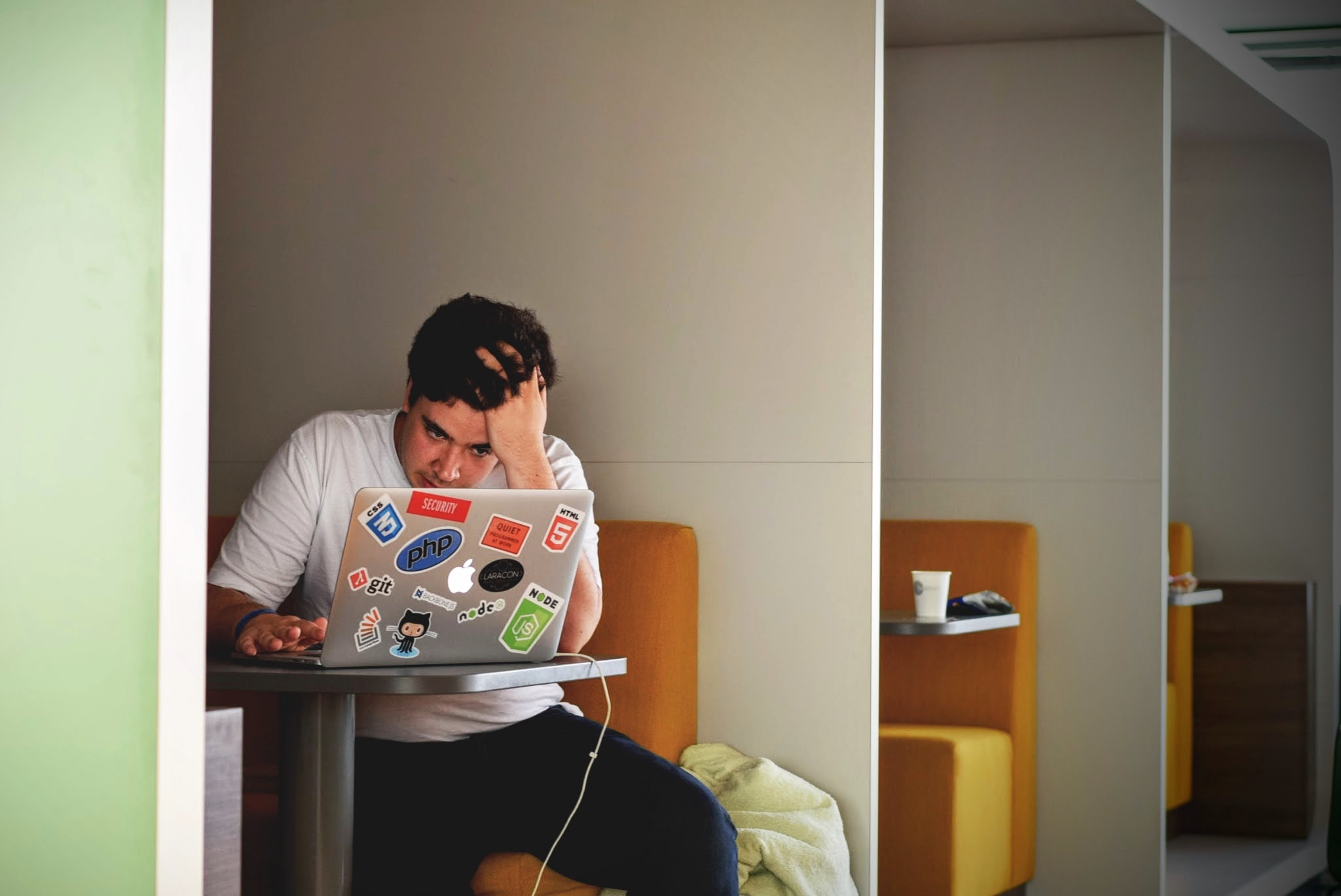
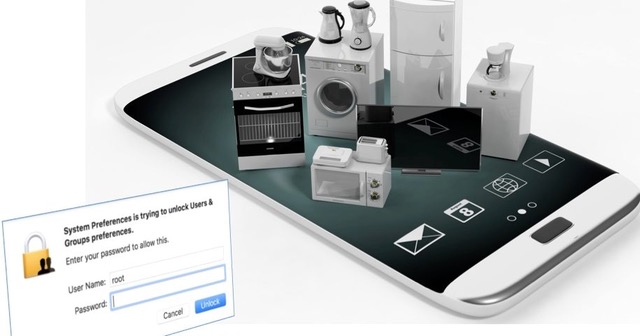
Overcoming the challenge of engaging employees in cyber security training is crucial for minimizing risk exposure.
Click Armor® addresses this by offering interactive, gamified training solutions, which increase participation, enhance knowledge retention and prepare employees more effectively for defending against cybersecurity threats.
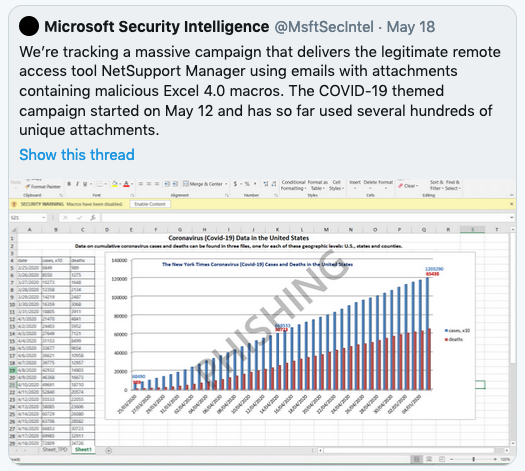
News & Insights
The latest Click Armor news and expert insights to help you fight phishing, social engineering scams and other risks related to human behaviors.
Featured in

Maximizing Employees’ Cyber Security Engagement and Resilience
Discover How Click Armor Transforms Training

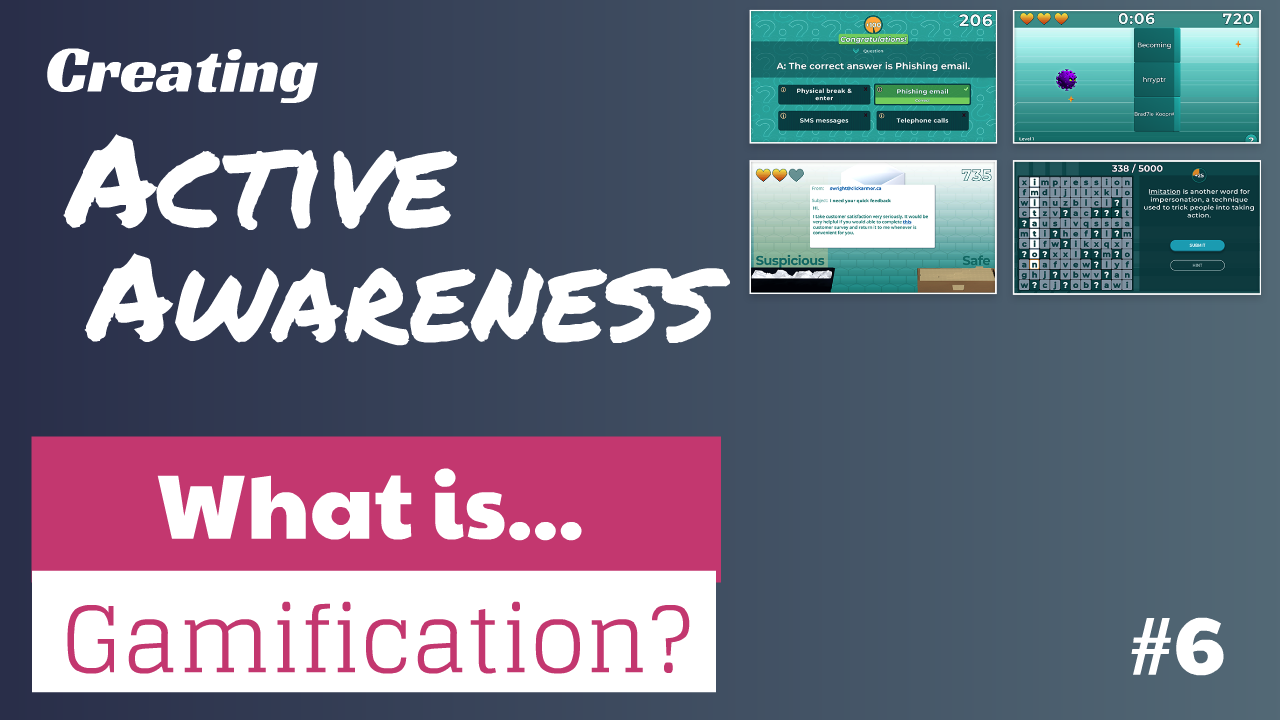
Engaging, Gamified Learning
Tap into Psychological Drivers to Increase Employee Engagement and Motivation
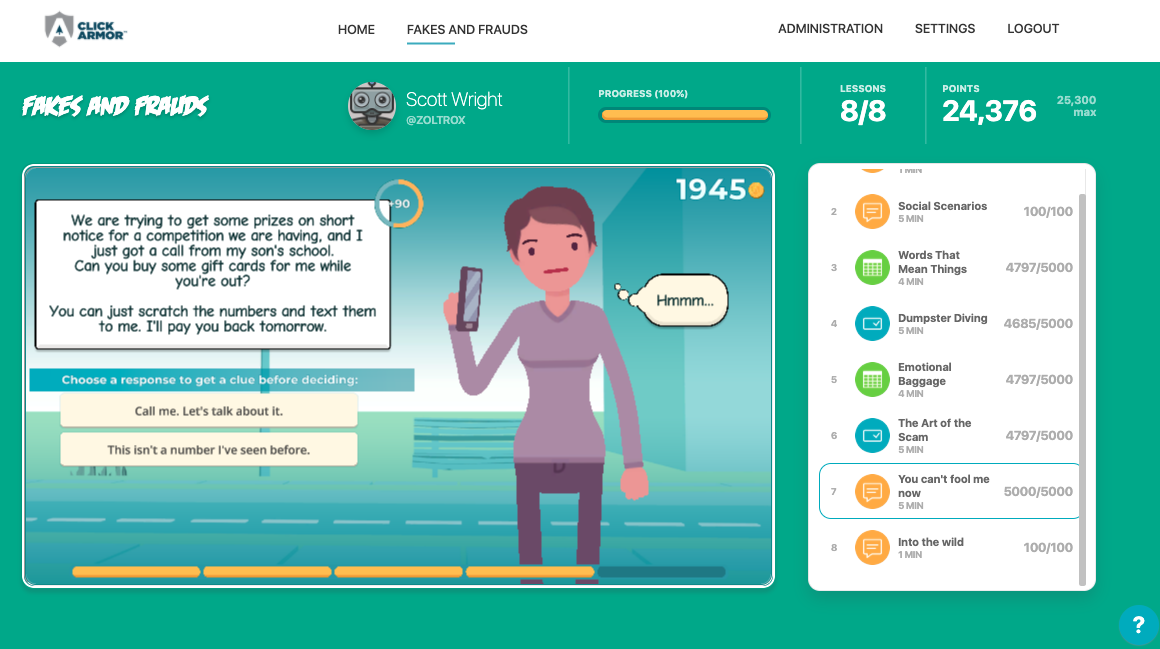
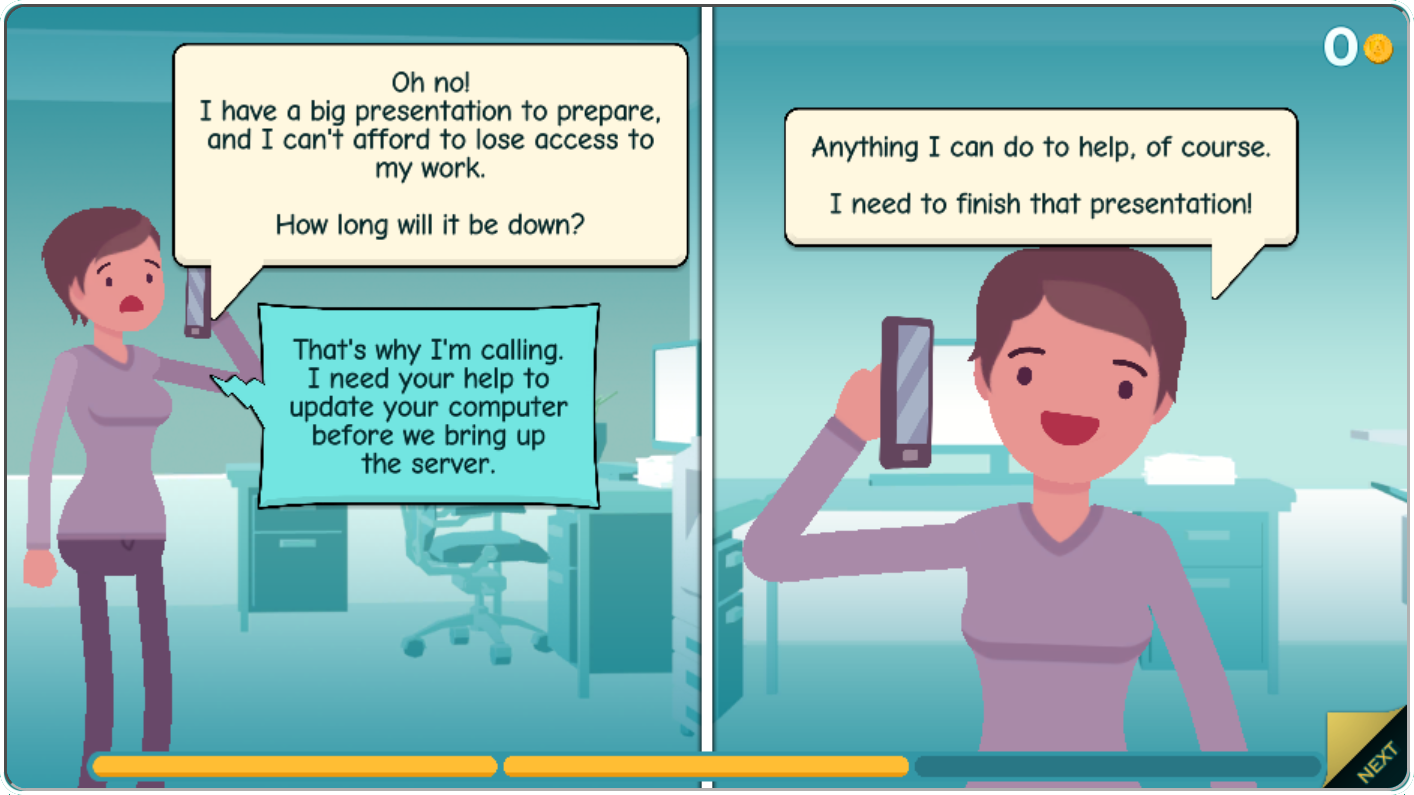
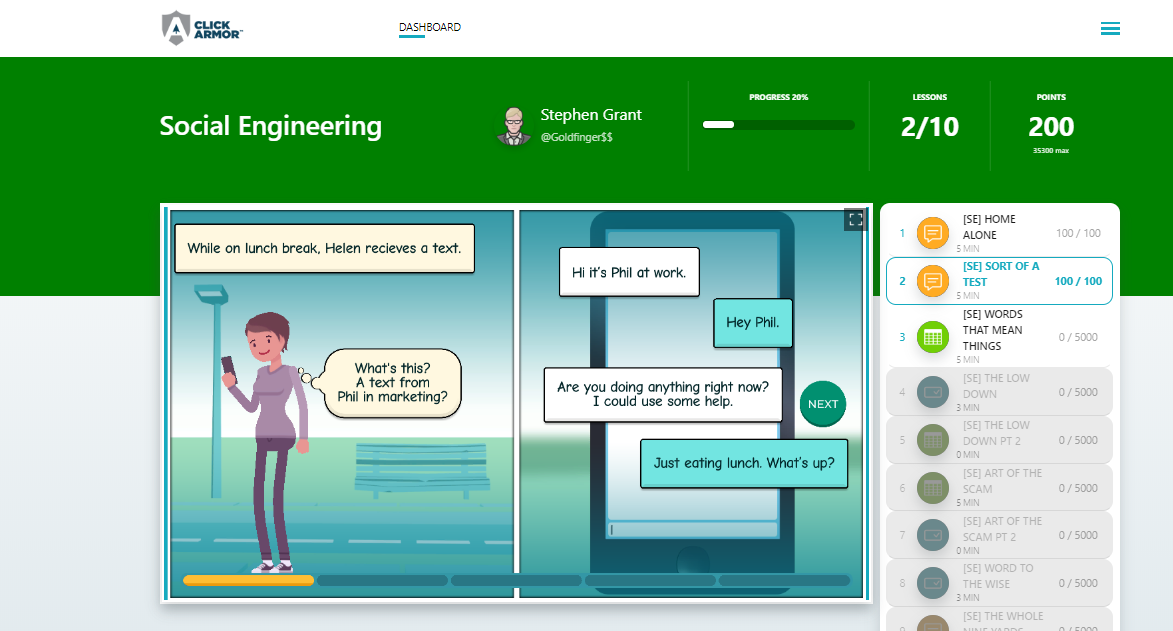
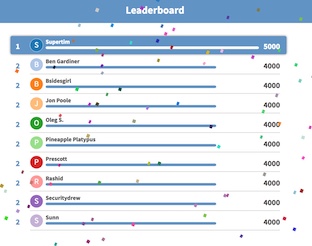
By leveraging interactivity and game-based learning, Click Armor transforms the traditionally mundane task of cybersecurity training into an engaging, interactive experience. This approach taps into the natural human love for enjoyable challenges, games and competition, increasing employee engagement and motivation.
Scalable Solutions
Provide Consistent and Effective Training, Regardless of Organization Size or Complexity
The scalability of Click Armor is a significant benefit for organizations of all sizes.
This ensures that as a business grows or changes, its cybersecurity training program can grow and change with it, providing consistent and effective training to all employees, regardless of the size or complexity of the organization.

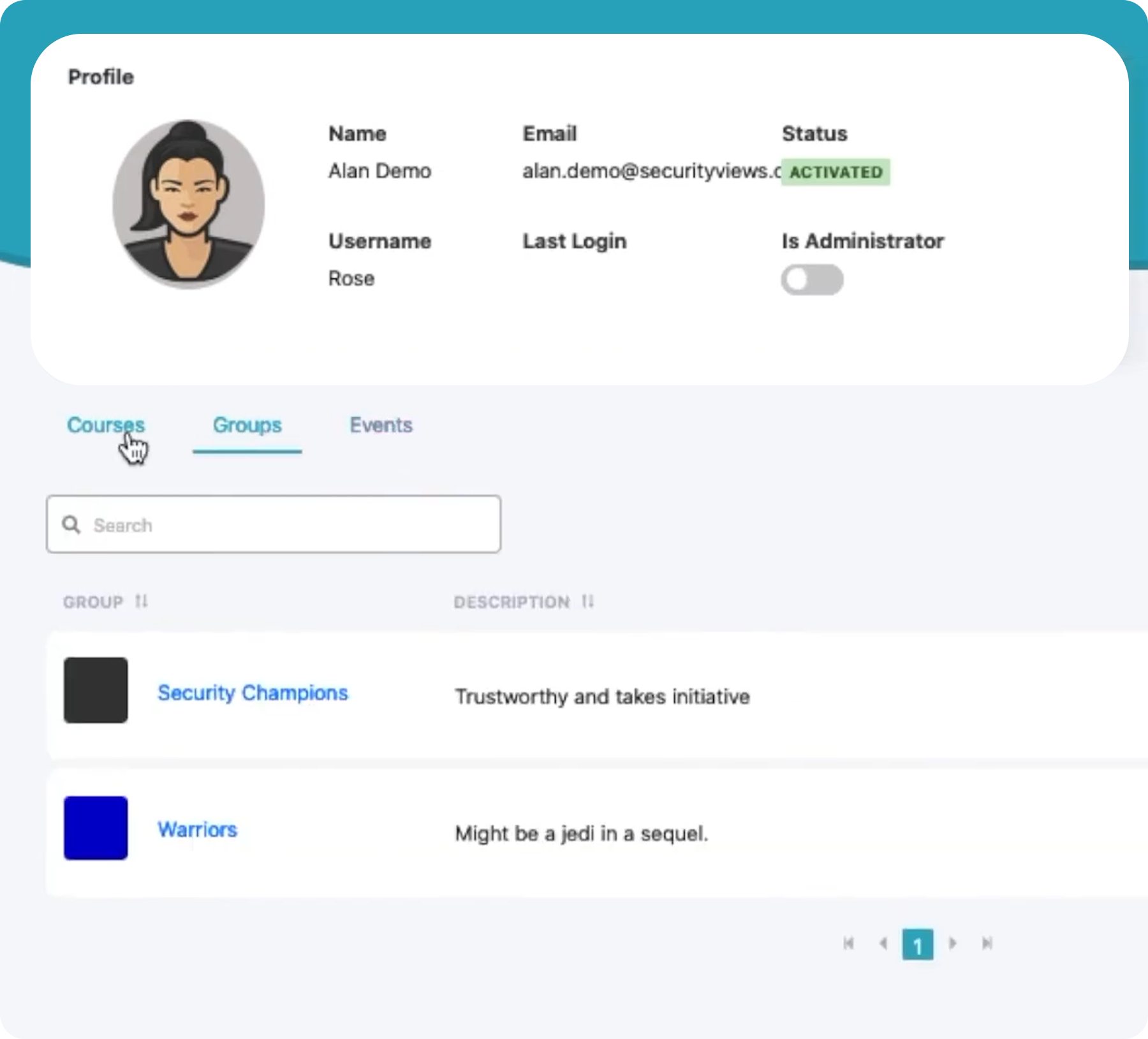
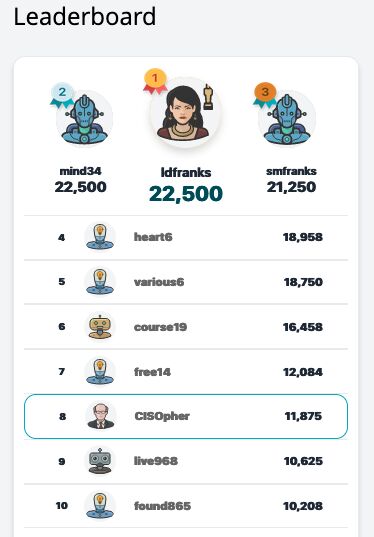
Real-Time Feedback and Analytics
Monitor Employee Progress and Identify Specific Areas where Additional Training is Needed
Click Armor offers comprehensive real-time feedback and analytics, enabling organizations to closely monitor employee progress and identify specific areas where additional training is required.
This is crucial for adapting cybersecurity training to evolving threats and personalizing training paths to ensure that employees are always up-to-date with the latest security practices they need for their roles.
Who is Click Armor for?
Click Armor is designed for organizations that prioritize the protection of sensitive data and systems from threats that target employees.
From engaging CEOs and CFOs with ROI-focused solutions to providing IT Directors with technically superior and efficient training platforms, Click Armor meets the unique demands of each sector.
Its customizable and scalable platform is ideal not just for information-based corporations, healthcare organizations, and financial institutions requiring compliance, but also for smaller businesses and owner/operators seeking comprehensive, cost-effective cybersecurity education.
Whether you need to help employees identified as vulnerable from assessments, or to focus on high risk roles with customized, interactive content, Click Armor has the most effective solution.
Click Armor is a versatile tool, essential for any entity serious about bolstering its defenses against cyber threats like phishing and social engineering.


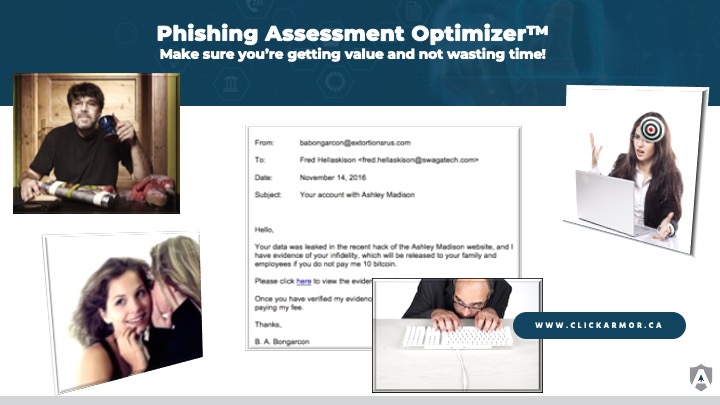
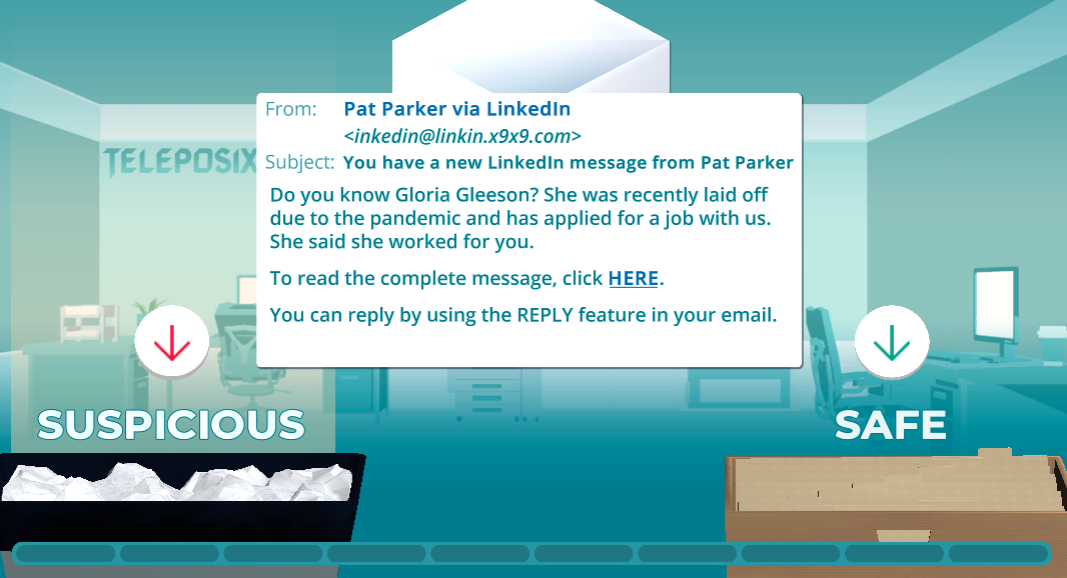
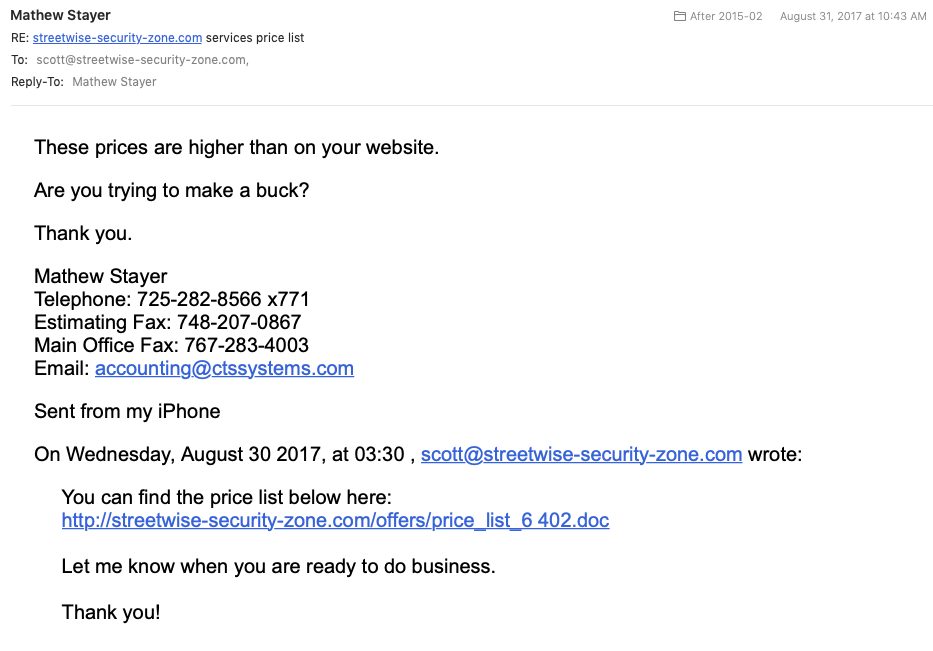
Test Your Cybersecurity Savvy
Take Our Quick 2-Minute Challenge!
Curious about your cybersecurity awareness? Dive into our interactive 2-minute, immersive phishing assessment! It's a fun, insightful way to gauge your current knowledge, in a way that illustrates the power of gamified learning for cyber security training.
Clients
What our clients have said about Click Armor: