December 20, 2024
The cyber attacks of 2024 were memorable to say the least. This year, cybercriminals targeted critical industries and high-profile organizations, using increasingly sophisticated tactics to exploit […]
December 11, 2024
The digital currency market is booming, and as security professionals, we must address the crucial question: Is crypto safe? Following the re-election of former President Donald […]
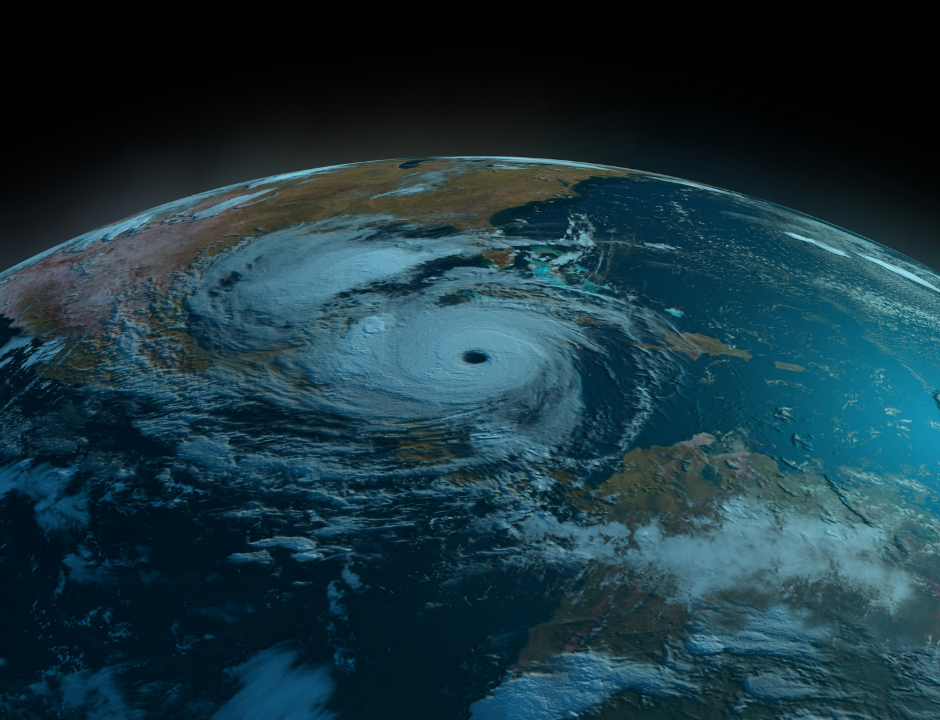
October 21, 2024
During national weather emergencies, many turn to online platforms to get the latest news but don’t know about the threat lurking in the weeds: Hurricane scammers. […]