
Why having backups may give you a false sense of security
Just because you have backed up all of your important data doesn’t mean that a ransomware attack can’t cause severe consequences for you. Up until now, most people have felt that the worst that could happen is to lose access to their data if they are hit by a ransomware attack.
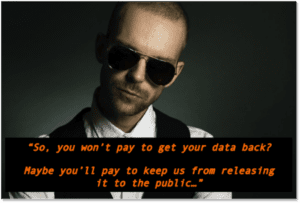
But a recent shift in tactics by attackers is making people think twice about not paying up. While you may not care about getting access to the data they’ve encrypted, they are betting there is still a lot of value in that data. And they might be right.
 If they can encrypt your data, they can do anything with it
If they can encrypt your data, they can do anything with it
Think about all of the data on your computer, and what the impact might be if it were made public or given to certain people. Perhaps there is financial information, login details to important websites you use, or even potentially embarrassing content or messages you wouldn’t want others to know about.
If the attackers can access your drive to the extent that they can encrypt all the data, there’s no reason they can’t copy the data before they encrypt it. Now, do I have your attention?
It’s a much bigger problem than you might think
How many press releases have you seen about ransomware breaches experienced by organizations that say, “There is no evidence that any of the affected information has been abused in any way.” This is a legal defence mechanism to ease people’s concerns about the risks to them. It is a very weak argument, as the attacker may well intend to use the data for extortion if the organization doesn’t pay… or maybe even if they do pay.
I call this “double dipping”. You might not need to pay the ransom to get access to the data they’ve encrypted, but you might very well want to pay to keep it from being disclosed to others. And once they have your data, they might keep coming back to get paid not to release it again and again…
This is another very good reason to take extra precautions against becoming infected with ransomware in the first place. Once infected, your data might become an open book.
Click Armor ‘s gamified phishing awareness course is a great way to learn about how to avoid clicking on dangerous links that can lead to ransomware infections.
A good example of how much damage this can cause is illustrated in the Sony Pictures security breach and data disclosures.
[/et_pb_text][/et_pb_column][/et_pb_row][et_pb_row _builder_version=”4.4.6″][et_pb_column _builder_version=”4.4.6″ type=”4_4″][et_pb_post_nav prev_text=”Previous Post” next_text=”Next Post” _builder_version=”4.4.6″ title_text_color=”#ffffff” background_color=”rgba(14,79,136,0.68)” custom_padding=”5px|10px|5px|10px|true|true” border_radii=”on|4px|4px|4px|4px” border_width_all=”1px”][/et_pb_post_nav][/et_pb_column][/et_pb_row][/et_pb_section]
